Earlier this year, I discovered that some WebDAV folders at my job were not configured securely. Long story short, it was bad. Not Everyone has access to Everything bad, but close. WebDAV is basically a file share served up by a web server (see the Wikipedia article on WebDAV for more details). If WebDAV is not configured securely, you are open to data theft, server compromise, and probably a lot more. I found some good information about securing WebDAV in various places and thought I would collect what I found in this post.
First, it is important to understand that WebDAV is used by almost every platform (Linux, Windows, etc.) and web server (Apache, IIS, etc.). I work primarily with Windows servers and IIS, so that is where most of the focus will be for this post. But the main ideas and techniques can be applied to any web server technology.
Second, securing WebDAV works in much the same way as securing any other web service. You apply the Policy of Least Privilege to reduce your attack surface. In many default configurations, WebDAV is open to everyone to perform any action. Who has access to WebDAV and what they can do must be restricted. The rest of this post will deal with how to do that, so let’s get started.
Restricting WebDAV Folder Access
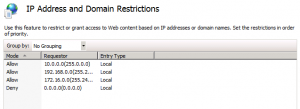
When setting up a WebDAV site or folder, it is important to know what access is needed. Will external IPs need access? Or will this be an internal-only WebDAV folder? If possible, it is best to restrict what IPs have access to your WebDAV folder. In IIS, this is done using IP Address and Domain Restrictions. In the example below, all of the private IP ranges are allowed and all other IPs are blocked.
Folder Permissions
If a non-anonymous form of authentication is used (and it should), access to WebDAV can be restricted further by using folder permissions. (For more information about using various authentication types with WebDAV, see this Microsoft TechNet article) Modify the NTFS permissions on the folder to only allow the access necessary to the users who require such access. If a certain group only needs read, only give them read. If another group needs create and modify, give them create and modify. This can be made very simple by creating a WebDAV_Read and a WebDAV_Write group in AD and assigning it to the WebDAV folder.
Preventing File Execution
If you are only using WebDAV as a file store and not using it to display web pages, then execute permissions should be removed from that site or folder. This will prevent web pages like .ASP or .PHP pages from being run from your WebDAV folder by an attacker. IIS6 and IIS7.x have different ways of preventing execution, so let’s discuss each.
Prevent File Execution in IIS6
In IIS6, you open IIS Manager, open the Properties of a site or folder, and go to the Directories tab. In the Execute Permission dropdown box, select None.
Prevent File Execution in IIS7.x
IIS 7 and 7.5 use Handler Mappings to prevent or allow execution of files. Like IIS6, open IIS Manager and select a site or folder. Next, go to Handler Mappings. In the Actions menu on the right-hand side, select Edit Feature Permissions. Finally, uncheck the box next to Script. This will disable all executable mappings and prevent any file from running in that folder.
Restricting Web Methods or Verbs
WebDAV uses a few special HTTP methods (also called verbs). Most people are familiar with the HTTP methods POST, GET, HEAD, and PUT. But WebDAV uses two methods that can be particularly dangerous – MKCOL and MOVE. MKCOL is used to create a collection, like a directory. MOVE is used to move a file from one URI to another or to rename files. If an attacker has the ability to upload files to the WebDAV folder, the MOVE command can be used to rename a harmless looking .TXT file to .ASP or .PHP or .EXE. That file can then be run on the server to open a backdoor for further exploitation. Be sure to read about SensePost’s ReDuh for an excellent example of this.
The solution is to deny the use of dangerous verbs like MKCOL and MOVE. IIS 7 and 7.5 make this pretty easy through Request Filtering. IIS 6 requires the installation and configuration of URLScan.
IIS 7.x Request Filtering
As you are installing IIS 7.x, you can also install Request Filtering as an additional Role under IIS -> Security (see this Microsoft TechNet article for more details). Once Request Filtering is installed, select the WebDAV site or folder you want to apply the filter to, open Request Filtering, and go to the HTTP Verbs tab. Select Deny Verb from the menu on the right and put MKCOL in the text box. Perform that action again for the MOVE method. It should end up looking something like below:
Any request on that folder or site that tries to include the MOVE or MKCOL methods will now be denied.
IIS 6 URLScan
I’ll be the first to admit that I don’t know a lot about URLScan. But it appears that this is the only way to block HTTP methods in IIS 6. URLScan is a Microsoft extension for IIS 6 and above that allows HTTP requsts that match a set of criteria to be blocked. IIS.Net has a good overview of URLScan if you want to read up on what it does and how to use it.
From what I have read, the way to block HTTP verbs using URLScan is to modify the urlscan.ini file. First, the option UseAllowVerbs=0 must be set. Next, a new section called [DenyVerbs] needs to be created and a list of the denied verbs should follow. It should look something like this:
UseAllowVerbs=0
...
...
[DenyVerbs]
MKCOL
MOVE
For more information about urlscan.ini, please read this Microsoft TechNet article.
Conclusion
In addition to the above, there is just the common sense stuff like not running your web server under an Admin account, making sure your web servers are patched, making sure your external web servers are in a properly configured DMZ, developing policies to ensure that confidential or sensitive information is not uploaded to your WebDAV folder, and so on.
WebDAV can be a useful tool, but it must be secured. Hopefully this post and the links within can be of assistance to any admins needing to lock down a WebDAV installation. If you have any other ideas on how to secure WebDAV, please let me know in the comments.