Latest version of the script is here:
http://giuoco.org/security/http-screenshot-html-13/
About a month ago, the folks at SpiderLabs created an NMAP NSE script to grab a screenshot of any scanned hosts that were running web services. (Read about it here). The guys over at Pauldotcom were talking about the script and how it would be cool if it could output the results with links and full header information. I decided this would be a good opportunity for me to learn some Lua and do some cool things with NMAP.
I downloaded the http-screenshot.nse script from SpiderLabs and stitched it together with the http-headers.nse script from NMAP. Outputting to HTML was a little tricky. The problem is that I couldn’t figure out how to write something (like the HTML BODY tags) to an output file only once. The code within the NSE script is going to get called every time NMAP finishes a scan on a host and port. So I ended up just dumping the partial HTML code in a file. It needs to be wrapped with the HTML, HEAD, and BODY tags, but I created a little perl script to do that.
I also added a few features. The script can properly determine when a service uses SSL and creates appropriate page links. I also had it generate a screenshot using both the IP and the domain name if it was available. Some web site respond differently to a full domain name than they do an IP address.
Download the scripts – http-screenshot-html.zip from Google Code
The ZIP contains 2 files – http-screenshot-html.nse and bodyWrap.pl. Be sure to place the http-screenshot-html.nse script in your NMAP scripts folder.
So, how does it work? First, you need wkhtmltoimage. So go to their Google Code page and download the version appropriate to your platform. It’s probably a good idea to make sure the executable is in your path to make calling it within the script easier. If you need to modify the path, just search the script for “wkhtmltoimage” and update as appropriate. The NSE script itself is called like any other. It can take up to 4 script arguments:
- path: path to the request. Like /index.php. (Default is /).
- useget: set this to force GET request instead of HEAD requests
- outpath: path for all output (screenshots, files, etc.)
- outfile: name of the output file containing the HTML code. (Default is “body.txt”).
A typical call to the script would look like this.
nmap --script=http-screenshot-html --script-args=outpath=C:/my/test/,outfile=test01.txt 192.168.1.0/24
This will output all of the screenshot files along with the “test01.txt” file to the C:/my/test/ directory. Now the “test01.txt” file needs to be transformed into an actual HTML file. This can be done by hand or by using the bodyWrap.pl file I created. It takes 2 arguments: -i for input file, -o for output file.
bodyWrap.pl -i C:/my/test/test01.txt -o C:/my/test/screenshot.html
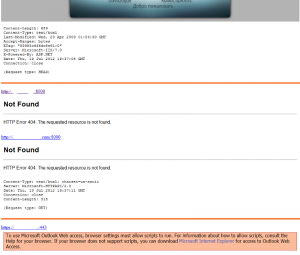
And that’s about it. When you are finished, the web page should look something like this.
As the screencap shows, you get screenshots of IP and host name (where available), appropriate links for SSL sites, and full headers.
One of the quirks of this script is that it will always append to the output file. If you run consecutive scans with “test01.txt” as your output file, it will simply append the new information to the file rather than overwrite it. So it’s always a good idea to output to an empty directory. I couldn’t figure out a way to create a new file every time the script was run. If someone knows how, please let me know.
Let me know what you think of the script. I’ll probably continue to tweak it here and there as I use it and think of more things to do.